Covid-19 is spreading continuously across the globe, causing fear and anxiety about the capacity of the healthcare systems, and on the other hand on the economy – our micro- and macro environment.
As staying at home and away from other people seems to be the most effective ’weapon’ to control the virus, organizations, schools and businesses are sending employees and students home to work and study. Our daily habit is changing completely therefore a totally new approach is needed, which is the use of the opportunities of the online world.
It is almost impossible to purchase new equipment to provide support to the employees these days, therefore those companies who allow their people to work on their own devices are facing real threats, as usually, these computers lack the companies’ protections (such as firewalls and restrictions).
We must be aware that the spread of the virus offers an opportunity for hackers to send emails with malicious attachments or links to fraudulent websites to trick victims into revealing sensitive information or donating to fraudulent charities or causes.
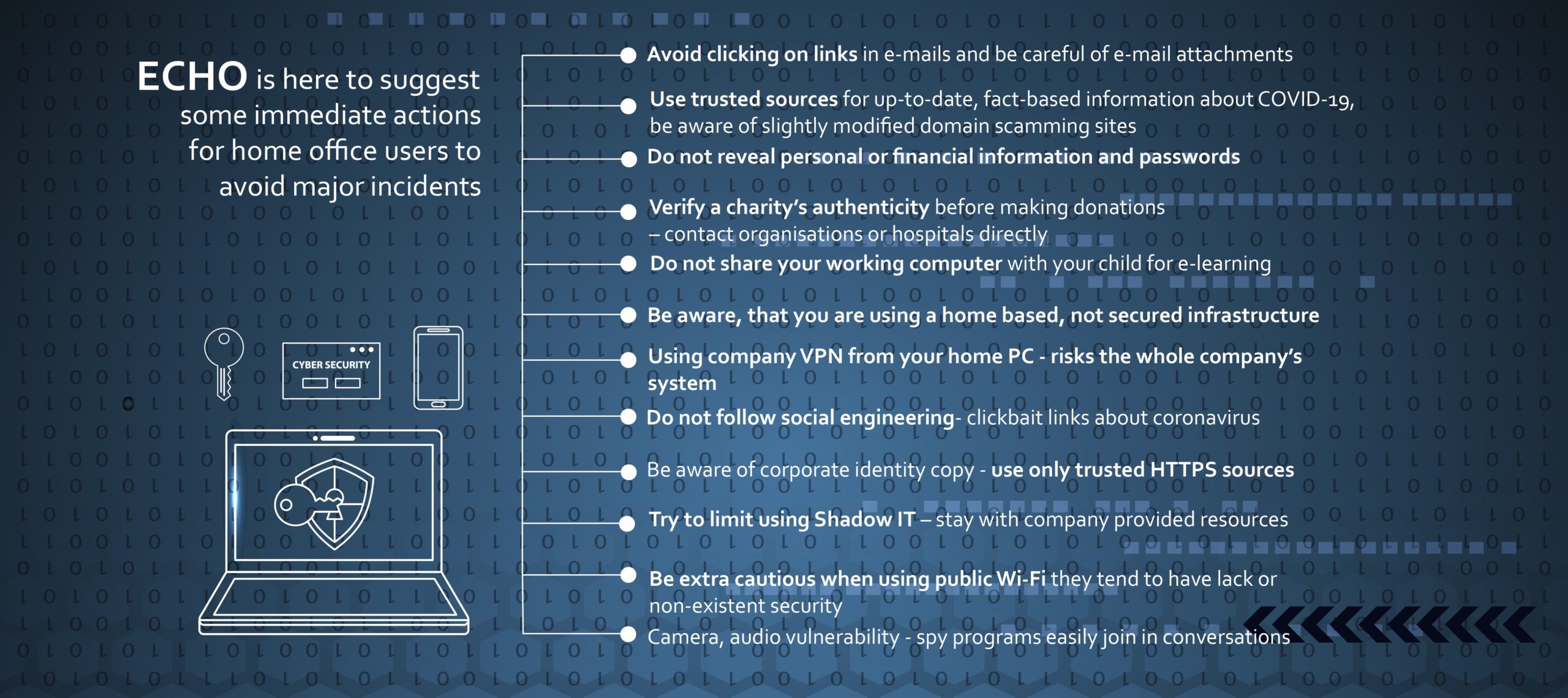
ECHO is here to suggest some immediate actions for home office users to avoid major incidents:
- Avoid clicking on links in unsolicited emails and be careful of email attachments
- Use trusted sources—such as legitimate, government websites—for up-to-date, fact-based information about COVID-19, be aware of slightly modified domain scamming sites
- Do not reveal personal or financial information and passwords in e-mail or chat programs, and do not respond to email solicitations for this information
- Verify a charity’s authenticity before making donations – contact organisations or hospitals directly
- Do not share your working computer with your child for e-learning
- Be aware, that you are using a home based, not secured infrastructure
- Using company VPN from your home PC – risks the whole company’s system if you do not keep the provided rules
- Do not follow social engineering – clickbait links about coronavirus
- Be aware of corporate identity copy – use only trusted HTTPS sources
- Try to limit using Shadow IT – stay with company provided resources
- Be extra cautious when using public Wi-Fi if you’re working on the go. Public Wi-Fi tends to have lack or non-existent security – leaving the network and your computer vulnerable to hackers
- Camera, audio vulnerability – spy programs easily join in private or corporate conversations
The pandemic has created a perfect storm for cyberattacks, with millions of people working in unfamiliar and less secure circumstances and eager for information about the virus and new organizational policies being implemented.