For most cyberattacks, malware is the component that delivers the decisive blow to the victim. Regardless of the increased capabilities of the attackers in delivering the attack or avoiding detection, the malware plays an important role in the success (or failure) of the attack. A first time introduced malware, or a new version of known malware, can achieve its objectives while remaining undetected by the in-place detection mechanisms and cybersecurity measures.
The impact of such incidents is rendering malware analysis a critical part of the defence against malware. A successful analysis of a malware sample can determine the structure, behaviour, ownership, lineage, and relations with other malware. This outcome can consequently estimate the potential impact of its operation inside a targeted infrastructure. The malware analysis results can become valuable assets in the adverse environment that constitutes the rapidly changing threat landscape. This information can and should be disseminated among teams and organisations that suffer from similar threats and attacks.
The correct, accurate and timely sharing of malware intelligence with other parties is imperative for identifying the relationships between malware and its authors. It is of paramount importance to attribute malware authors’ use of personas or even Advanced Persistent Threat (APT) groups that use their uniquely designed malware to wage cyber campaigns against nations or major enterprises to gain a proactive stance against them.
The attribution of malware to specific APT groups is a task that faces a series of technical challenges for the analyst. These challenges can be iterated as the architecture and the geography of the Internet, the lack of source code, the obfuscation techniques, the fake traces of authorship, spoofed IP addresses or even legal issues related to the operation of the APT groups and their sponsors.
In the effort to tackle these challenges, Cyber Threat Intelligence (CTI) can aid in extracting and analysing information from malware so that threat analysts can share it with consortiums. To guide the researchers in this field, our effort in ECHO introduces the Malware Analysis and Intelligence Tool (MAIT).
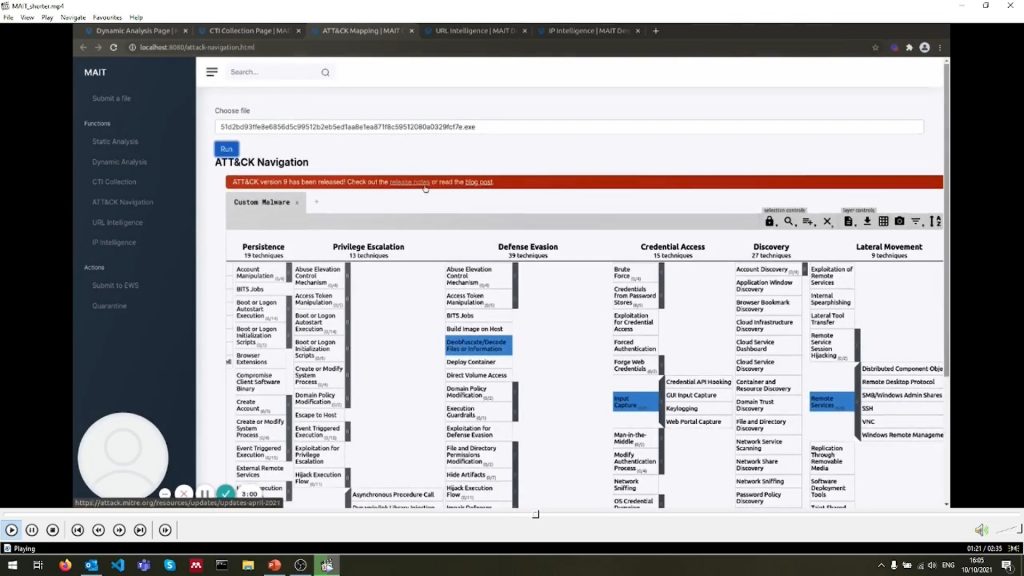
- MAIT uses state-of-the-art malware analysers (static and dynamic) combined with open-source malware databases to provide a malware signature and an intelligence report collected from public sources.
- The tool is seamlessly integrated, in the form of a cyber ticket, with the Early Warning System (EWS) built for the European network of Cybersecurity centres and competence Hub for innovation and Operations (ECHO) as a platform for secured collaborative information sharing of cyber-relevant information.
- With the use of MAIT, the user of the EWS can use any malware executable as input in order to retrieve a report containing information consisting of the following:
- Chronological data about the malicious file, i.e., first appearance, increase in time.
- Any weaponisation in any APT campaigns or cyber-attacks in general.
- Public information on cyber attribution.
- Related vulnerabilities and information.
If you wish to know more about MAIT, watch the demonstration video on ECHO's YouTube channel here:





